When a user connects to a VPN server, a “tunnel” is created. This is done by the VPN server forming an encrypted link with the user’s computer.
 Checkout this video:
Checkout this video:
Introduction
When you connect to a VPN, “tunneling” is used to send your traffic through an encrypted connection to the VPN server. This keeps your data safe from eavesdroppers and protects your privacy. There are different types of tunneling, and each has its own advantages and disadvantages.
Tunneling can be divided into two main categories: layer 2 tunneling and layer 3 tunneling. Layer 2 tunneling protocols (L2TP) send traffic through an encrypted tunnel at the data link layer (layer 2). Layer 3 tunneling protocols (IPsec and OpenVPN) send traffic through an encrypted tunnel at the network layer (layer 3).
Layer 2 tunneling protocols are typically faster than layer 3 protocols because they don’t have to go through the extra step of encapsulating each packet in an IP header. However, L2TP is more susceptible to security attacks than IPsec or OpenVPN.
Layer 3 tunneling protocols are more secure than layer 2 protocols, but they can be slower because each packet has to be encapsulated in an IP header. IPsec is typically used with IKEv2 for better security, while OpenVPN is usually used with SSL/TLS for better speed.
What is a VPN?
A VPN, or Virtual Private Network, is a technology that allows you to create a secure connection over a less-secure network. For example, you can use a VPN to connect to the internet over a public Wi-Fi network, or from your home computer over your ISP’s unsecured network.
VPNs are often used by businesses to allow employees to securely connect to the company network from remote locations. They are also used by individuals who want to protect their privacy, such as when using public Wi-Fi networks or when accessing region-locked content.
When you connect to a VPN, all of your traffic is routed through an encrypted tunnel to the VPN server. This encrypts your traffic and hides your IP address, preventing third parties from seeing what you’re doing online.
What is tunneling?
In computer networks, a tunnel is simply a logical connection between two networked devices. When data is sent over a tunnel, it is encapsulated within another data packet so that it can be routed through the second device and onward to its destination. Tunnels are commonly used to extend networks or connect remote users to a central network.
There are two main types of tunnels: point-to-point and multipoint. Point-to-point tunnels are typically used to connect two devices, while multipoint tunnels can connect multiple devices. Multipoint tunnels are further divided into static and dynamic multipoint tunnels. Static multipoint tunnels are preconfigured between devices, while dynamic multipoint tunnels are set up on demand as needed.
Tunneling protocols such as the Layer 2 Tunneling Protocol (L2TP) and Internet Protocol Security (IPSec) can be used to create both point-to-point and multipoint tunnels. L2TP is commonly used in conjunction with IPSec to create Virtual Private Networks (VPNs), which provide secure, encrypted connections over public networks such as the Internet.
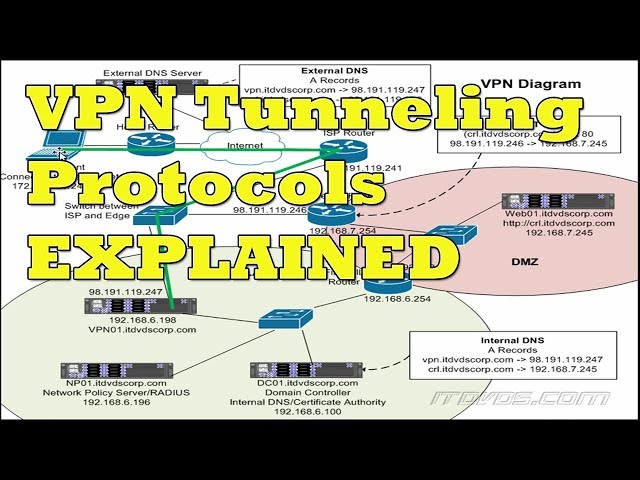
How is tunneling accomplished in a VPN?
A Virtual Private Network (VPN) provides a secure and private connection over a public network, such as the internet. VPNs can be used to access region-restricted websites, shield your browsing activity from prying eyes on public Wi-Fi, and more.
Tunneling is a method of encapsulating Internet Protocol (IP) datagrams within packets of the same IP protocol for transmission over an intermediary network, such as the public Internet. When you connect to a VPN, all of your traffic is sent through a secure tunnel to the VPN server. This encrypts your data and prevents anyone from snooping on your traffic, ensuring your privacy and security.
Conclusion
In conclusion, we have seen how tunneling is accomplished in a VPN. We have also looked at the different protocols that are commonly used in VPNs. Finally, we have seen how tunneling can be used to provide security and privacy for users of a VPN.
